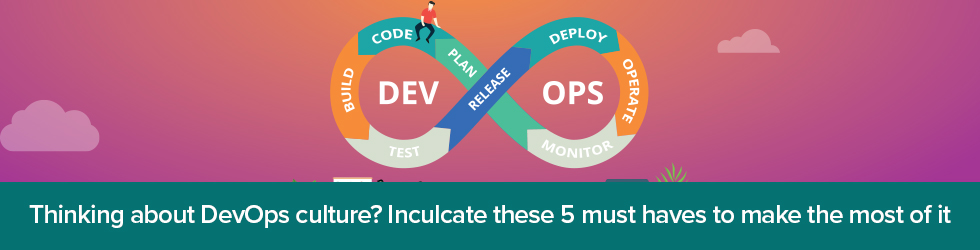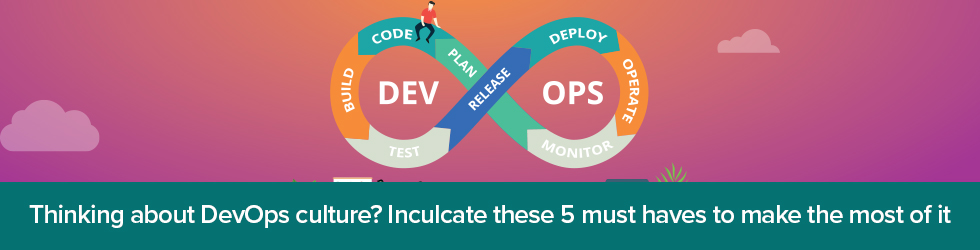
Digitalization has reached a new level, especially as the demand for better experiences has increased. In order to develop and deploy their software production, brands are constantly making use of DevOps to streamline their production cycles and make them more robust.
Let’s discuss what DevOps is all about, and how accepting the DevOps culture can help an organization achieve its goals in the best possible manner.
What is DevOps?
DevOps can’t be classified as a “thing” per se—it’s a set of principles that are necessary for laying the foundation of the developer culture. When one talks about objectives, the first thing that comes to mind is that DevOps is a methodology that is used to speed up the time to market, and further apply incremental improvements within the software space.
DevOps is a set of principles geared towards cross-training a multitude of teams involved in software development and infrastructure operations. In other words, it is a domain responsible for the design, deployment and maintenance of continuous integration and continuous delivery, or CI/CD frameworks.
The best way to integrate the two streams is by involving the development team and the operations team. This way, a channel of communication is opened, fostering a partnership between the two teams. In order to facilitate such communication channels, here is a list of key principles that need to be incorporated to find success in the DevOps space.
Foster a Collaborative Environment
The first and most important principle behind DevOps is the successful collaboration between the operations and the development teams. By creating a unilateral team, the DevOps team can focus on delivering the organization’s common goals and achieve its purpose. The fundamental idea behind this concept is to ensure both the team work together and communicate with each other so that they can share ideas and solve problems together.
This way, one can break down silos and align their people, processes, and technology towards achieving organizational goals. By aligning processes, such specialized teams can create a fluid experience, which can facilitate a culture of developments and deployments across the whole organization.
Create a culture to sustain end-to-end responsibility
Traditionally, developers and operations worked separately, within limited to no interaction between the different teams. However, in the DevOps environment, both teams are forced to work together to achieve the common goals and work as a centralized team. Nevertheless, with the shift in the DevOps culture, there is a different approach to this concept. Inefficiencies are addressed, plus there is a place for everything and everyone within the teams.
Facilitate continuous improvement
With added end-to-end responsibility, there is an additional need to adapt to the changing circumstances in order to evolve with the emergence of new technology, customer needs and any shifts in legislation.
DevOps focuses on continuous improvement, which is aimed at optimizing performance, speed, and cost of delivery.
Automate everything possible
Automation has become the need of the hour. As there is a growing awareness amongst consumers, continuous improvement is needed to meet customer demands. Keeping this thought in mind, there have been notable developments with respect to adopting tools that support automaton, as well as in streamlining the processes which include configuration management, the CI/CD pipeline, and more.
Throughout the automation process, several processes can be automated to perform efficiently with the given resources. This would include infrastructure provisioning, building new systems, software development and deployment, as well as conducting various tests that pertain to functionality and security compliance.
Through DevOps, teams can develop their own automated processes aimed at reducing the development and deployment turnaround time. Machines can be trained efficiently to deploy software quicker than their usual turnaround time, while keeping their reliability intact.
Focusing on customer’s needs
Brands that don’t innovate continuously can’t survive their customer’s demands. For this very reason, brands need to act like a lean startup, which need to innovate as the time changes. DevOps teams must always be on the move to meet their customer’s requirements. The data gathered from the automated processes can be analyzed to check if performance targets are met, which would ultimately delivery customer satisfaction.
Schedule Your Free DevOps Assessment